GitHub CVE-2026-3854 Enables Remote Code Execution via Single Git Push
Key Takeaways
- CVE-2026-3854 enables remote code execution (RCE) through a single git push
- Improper sanitization of Git Push options leads to command injection
- GitHub.com and GitHub Enterprise Server are both affected
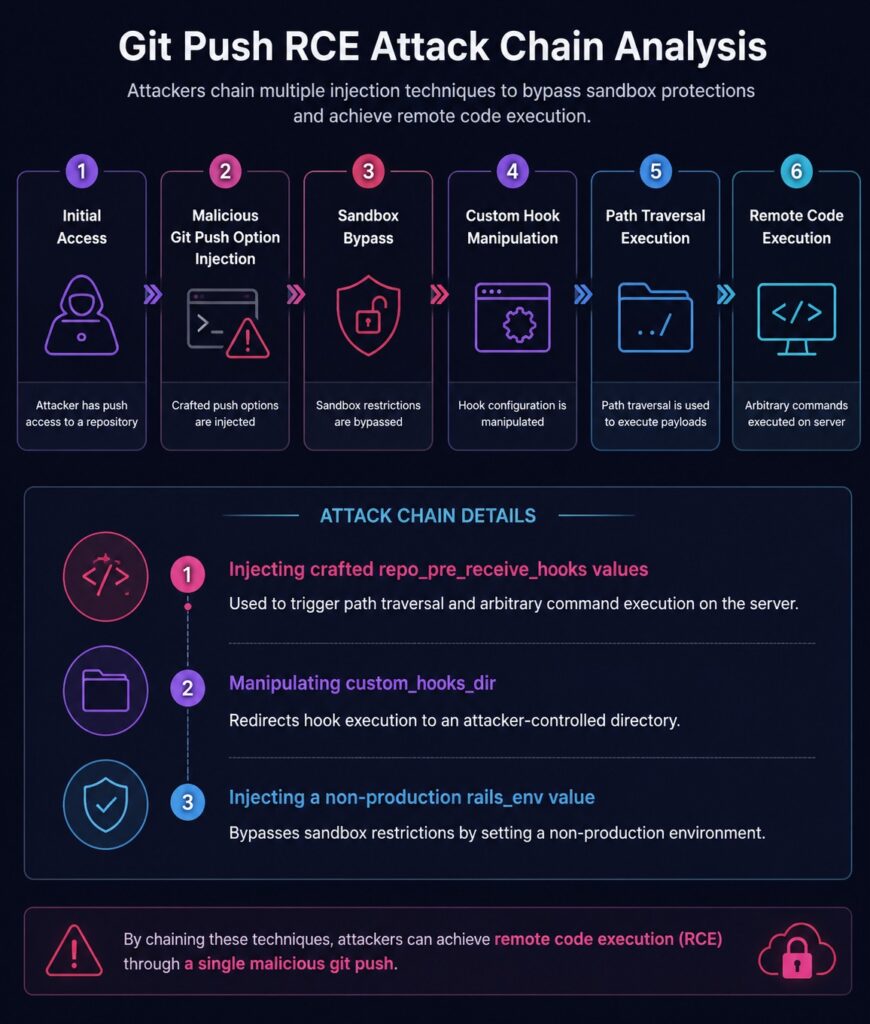
- Attackers can bypass sandbox protections through crafted metadata injection
- Multi-tenant environments face potential cross-repository exposure risks
- Immediate patching is strongly recommended
Critical GitHub RCE Vulnerability Disclosed
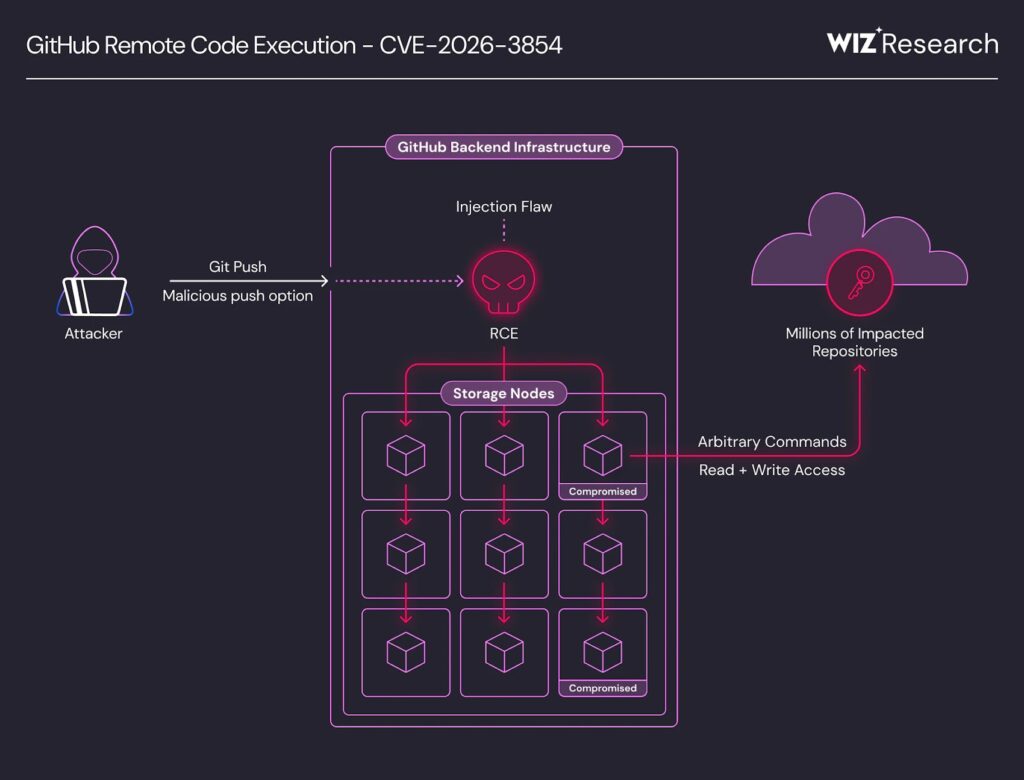
Security researchers have disclosed a critical remote code execution (RCE) vulnerability, tracked as CVE-2026-3854, impacting GitHub and GitHub Enterprise Server environments.
The vulnerability allows an authenticated attacker with repository push access to execute arbitrary commands on the server using a single git push command.
The issue was discovered by Google-owned cloud security company Wiz, with GitHub reportedly deploying a fix to GitHub.com within two hours of validation.
CVE-2026-3854 Command Injection Vulnerability Analysis
The vulnerability originates from insufficient sanitization of user-supplied Git Push option values during internal metadata processing.
GitHub internally processes push option values through the X-Stat header format. However, because the metadata structure relies on semicolon (;) delimiters that could also be included within user input, attackers could inject additional metadata fields and manipulate internal service behavior.
Researchers demonstrated that carefully crafted push options could ultimately lead to arbitrary command execution on backend infrastructure.
Git Push RCE Attack Chain Analysis
Multi-Tenant GitHub Environment Exposure Risks
The impact becomes more severe within GitHub.com’s multi-tenant architecture.
Researchers noted that successful code execution could provide attackers with:
- Filesystem read/write access
- Internal service configuration visibility
- Shared storage node access
- Repository exposure across organizations
GitHub stated that exploitation within shared back-end infrastructure could potentially expose millions of repositories hosted on affected storage nodes.
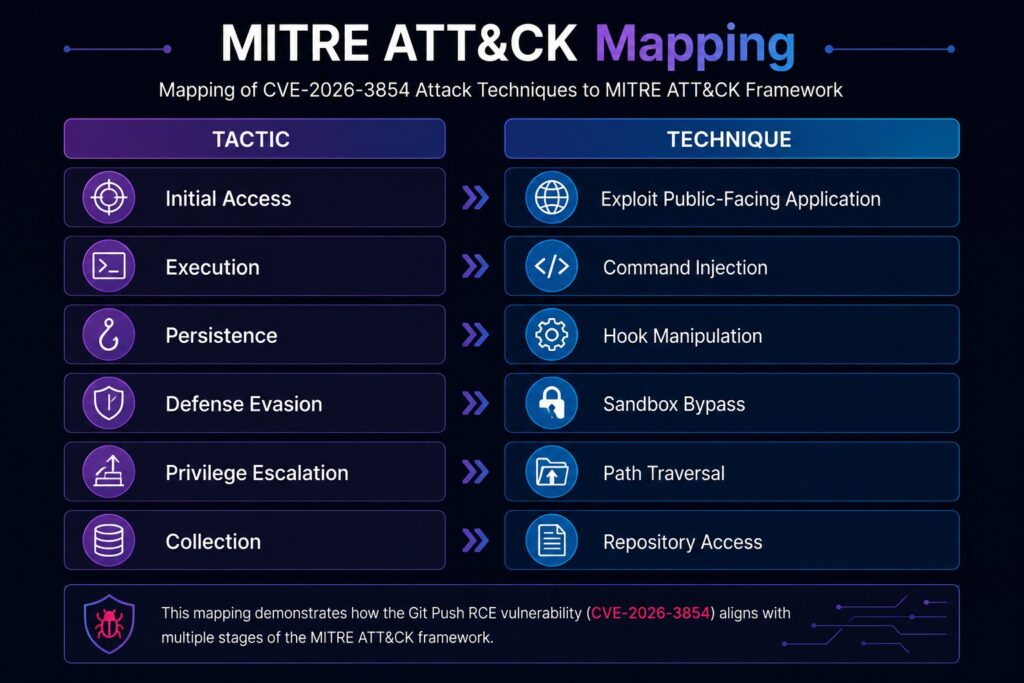
MITRE ATT&CK Mapping
Affected GitHub Enterprise Server Versions
GitHub addressed the vulnerability in the following versions:
- 3.14.25
- 3.15.20
- 3.16.16
- 3.17.13
- 3.18.8
- 3.19.4
- 3.20.0 and later
Although no evidence of malicious exploitation has been identified, Wiz estimated that approximately 88% of instances were vulnerable at the time of public disclosure.
WSS Detection Points
- Suspicious Git Push request activity
- Command injection pattern detection
- Unauthorized hook directory modification attempts
- Abnormal path traversal behavior
- Unauthorized server-side command execution
Growing Risks from Internal Protocol Attack Surfaces
This incident highlights how internal protocols within multi-service architectures can become critical attack surfaces when user-controlled input is insufficiently validated.
As modern development platforms rely on increasingly complex service interactions and metadata processing, attackers are shifting focus beyond traditional web vulnerabilities and targeting internal trust boundaries and protocol assumptions.
Organizations operating Git-based DevOps environments should strengthen monitoring and validation controls surrounding internal automation workflows and hook execution mechanisms.
Importance of Security Monitoring in Git-Based DevOps Environments
The GitHub CVE-2026-3854 vulnerability demonstrates how development and DevOps infrastructure are becoming increasingly attractive targets for sophisticated attackers.
As Git-based automation, hooks, and internal service integrations grow more complex, organizations must implement real-time monitoring and anomaly detection capabilities to identify abnormal command execution and injection attempts.
Solutions such as WSS can support detection of malicious request behavior, command injection attempts, and web-based attack activity.
Related Threat Intelligence
- Ivanti EPMM Vulnerability Exploited to Deploy Sleeper Webshells
- Linux Security Alert: Cookie PHP Web Shells (MS Report)
- Dell WMS Vulnerability: Defending Against JSP Webshells
- ASP.NET Web Shell Threats Targeting IIS Servers (UAT-8099 Case Study)
- BeyondTrust Flaw Used for Web Shells, Backdoors, and Data Exfiltration
- Web Shells and Lateral Movement
- Godzilla Webshell: A Growing Cybersecurity Threat to Healthcare
- The Evolution of the China Chopper
- APT41’s Cyber Espionage Campaign: Web Shells at the Core of Network Infiltration
Sources
News: Researchers Discover Critical GitHub CVE-2026-3854 RCE Flaw Exploitable via Single Git Push