Ivanti EPMM Vulnerability Exploited to Deploy Sleeper Webshells
1. Introduction
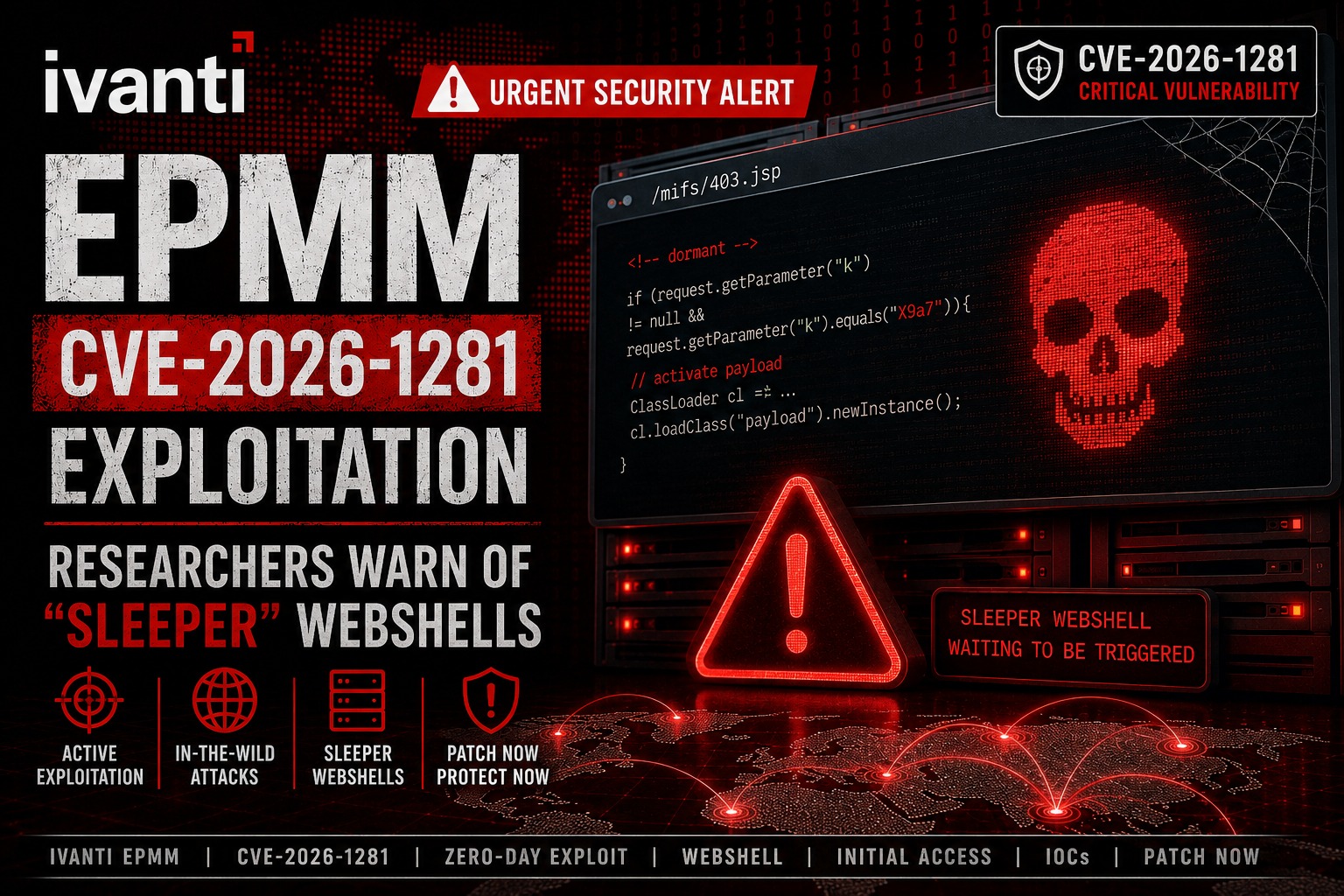
Security researchers have identified campaigns leveraging this flaw to deploy “sleeper” web shells which are malicious implants designed to remain dormant until triggered, allowing attackers to establish persistent and stealthy access to compromised systems.
A critical vulnerability in Ivanti Endpoint Manager Mobile (EPMM) is being actively exploited following the disclosure of CVE-2026-1281, with researchers warning of large-scale exploitation attempts.
2. Vulnerability Overview
CVE-2026-1281 is a pre-authentication code injection vulnerability affecting Ivanti EPMM. The flaw enables attackers to execute malicious code without requiring valid credentials, significantly increasing the risk of unauthorized access. The vulnerability was disclosed alongside CVE-2026-1340, with Cybersecurity and Infrastructure Security Agency (CISA) adding CVE-2026-1281 to its Known Exploited Vulnerabilities catalog on the same day, confirming active exploitation in the wild.
3. Attack Method and Technical Analysis
Researchers from GreyNoise and Defused Cyber observed multiple exploitation patterns following disclosure.
In one campaign, attackers deployed dormant in-memory Java class loaders to compromised EPMM instances at the path /mifs/403.jsp. These implants require a specific trigger parameter to activate, allowing them to remain undetected during initial compromise.
Additionally, GreyNoise identified exploitation sessions where attackers used lightweight payloads that “phone home” via DNS to confirm whether a target system is exploitable. These payloads do not immediately deploy malware or exfiltrate data but instead validate access for potential follow-on exploitation.
This behavior is consistent with operations conducted by initial access brokers, who prepare compromised systems for later use by other threat actors.
4. Impact and Risk
Successful exploitation of CVE-2026-1281 can result in unauthorized system access, persistent compromise, and the eventual deployment of additional malicious payloads.
The use of sleeper web shells significantly increases the risk, as these implants remain inactive until triggered, making detection more challenging. This delayed activation model allows attackers to bypass traditional monitoring systems that focus on immediate post-exploitation activity.
Several organizations have already been impacted, including government-related entities in Europe, highlighting the real-world consequences of unpatched systems.
5. Security Implications
The widespread exploitation of this vulnerability underscores the growing use of staged attack techniques, where initial access is established and validated before full exploitation occurs.
Organizations using Ivanti EPMM are advised to assume compromise and conduct thorough forensic investigations. Recommended mitigation steps include applying security patches, restarting application servers to remove in-memory implants, and reviewing logs for indicators of compromise.
In this context, advanced detection capabilities are essential to identify both active and dormant threats. Solutions such as WSS can support real-time detection of abnormal web shell behavior, including stealthy or delayed-execution payloads.
6. Conclusion
The exploitation of CVE-2026-1281 highlights how attackers are evolving their tactics to establish persistence while minimizing detection. As sleeper web shell techniques become more prevalent, organizations must adopt proactive monitoring and detection strategies to mitigate long-term risk.
7. Explore More Web Shell Threat Cases
- EncystPHP Web Shell Seizes 900 Servers Worldwide
- Linux Security Alert: Cookie PHP Web Shells (MS Report)
- Dell WMS Vulnerability: Defending Against JSP Webshells
- ASP.NET Web Shell Threats Targeting IIS Servers (UAT-8099 Case Study)
- BeyondTrust Flaw Used for Web Shells, Backdoors, and Data Exfiltration
- Web Shells and Lateral Movement
- Godzilla Webshell: A Growing Cybersecurity Threat to Healthcare
- The Evolution of the China Chopper
- APT41’s Cyber Espionage Campaign: Web Shells at the Core of Network Infiltration
8. Sources
- News: Ivanti EPMM exploitation: Researchers warn of “sleeper” webshells
- News: Ivanti provides temporary patches for actively exploited EPMM zero-day (CVE-2026-1281)
- News: European Commission hit by cyberattackers targeting mobile management platform
- Analysis Report: Someone Knows Bash Far Too Well, And We Love It (Ivanti EPMM Pre-Auth RCEs CVE-2026-1281 & CVE-2026-1340