ASP.NET Web Shell Threats Targeting IIS Servers (UAT-8099 Case Study)
Despite rapid advancements in security technology, web shells remain the preferred weapon for hackers. The UAT-8099 attack campaign, disclosed by research labs such as Cisco Talos on January 29, 2026, serves as a critical warning for organizations globally.
Many enterprises rely on Microsoft’s Internet Information Services (IIS) for their web services, and UAT-8099 capitalized on this. Rather than simple system destruction, they deployed sophisticated ASP.NET web shells to hijack server functionalities and maintain long-term, covert persistence. Below is an analysis of their tactics and how to reinforce server security.
1. UAT-8099 Attack Scenario: From Penetration to Takeover
The UAT-8099 operation was highly methodical and staged:
- Initial Compromise: Attackers exploited poorly secured file upload features. By bypassing filters, they successfully planted malicious web shells in .aspx format within the server.
- Privilege Escalation & Backdoor Establishment: Once installed, the web shell acted as an extension of the attacker, executing system commands. They forcibly enabled Remote Desktop Protocol (RDP) and created new administrative accounts to ensure a “dedicated backdoor” for future access.
- Persistence: The group utilized obfuscation and hid the web shells in directories difficult for traditional Anti-Virus (AV) solutions to scan, allowing them to remain undetected for extended periods.
2. Core Tool ‘BadIIS’ and SEO Fraud
A terrifying aspect of UAT-8099 is its use of the server as a “host” for secondary crimes. At the center is a custom malware known as BadIIS.
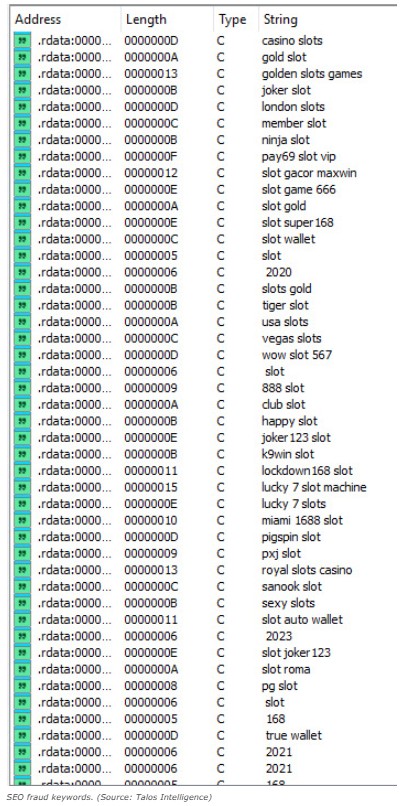
- Sophisticated Stealth: BadIIS manipulates how the IIS server responds to requests. While regular users see the legitimate website, Googlebot and other search engine crawlers are served malicious content or hidden advertisements.
- Business Impact: Legitimate websites are transformed into promotional hubs for gambling and spam. This severely damages brand reputation and can lead to the site being permanently blacklisted by search engines as a “dangerous site.”
3. Technical Countermeasures Against UAT-8099
Traditional perimeter security is insufficient because Web Application Firewalls (WAF) often cannot detect a web shell once it has bypassed the initial entry point.
- File Upload Security & Execution Restrictions: Organizations must strictly control file upload functionalities. Beyond restricting extensions, script execution permissions should be disabled in upload directories to prevent web shells from running.
- System Integrity & Process Monitoring: Since UAT-8099 often enables RDP or creates unauthorized accounts, real-time monitoring of system configuration changes and account creation is vital. Immediate alerts should be triggered for any unauthorized processes.
- IIS Configuration & Source Code Audits: Given that the attack involves hijacking IIS modules through ‘BadIIS,’ administrators should regularly audit the integrity of IIS module configurations. Periodic full-scale inspections of source code are necessary to identify injected scripts or external call logic.
4. The Strongest Defense: Identifying “Invisible Threats”
The UAT-8099 case demonstrates how a single web shell can compromise an entire infrastructure and ruin a business’s reputation. In 2026, as threats evolve, the key to protection is “visibility.” Establishing a system that monitors and responds to spies hiding inside the server is the only way to ensure business continuity.
Web security must move beyond simple blocking toward a “visual security” paradigm. Implementing real-time integrity monitoring that detects even minute changes in source code is essential. Protect your IIS servers proactively with WSS (Web Server Safeguard), which utilizes AI-based analysis to detect even the most advanced polymorphic web shells.
5. Explore More Web Shell Threat Cases
- EncystPHP Webshell Seizes 900 Servers Worldwide
- Linux Security Alert: Cookie PHP Web Shells (MS Report)
- Dell WMS Vulnerability: Defending Against JSP Webshells
- BeyondTrust Flaw Used for Web Shells, Backdoors, and Data Exfiltration
- Web Shells and Lateral Movement
- Godzilla Webshell: A Growing Cybersecurity Threat to Healthcare
- The Evolution of the China Chopper
- APT41’s Cyber Espionage Campaign: Web Shells at the Core of Network Infiltration