EncystPHP Webshell Seizes 900 Servers Worldwide
Earlier this year, a severe security incident occurred on FreePBX, an open-source IP PBX platform. The emergence of a “weaponized webshell” that goes beyond simple intrusion to neutralize system privileges and exfiltrate data has sent shockwaves through the security community. Today, we provide an in-depth analysis of the risks posed by the EncystPHP webshell and its countermeasures.
1. Vulnerability Swallowing Over 900 Servers
On February 27, 2026, the security outlet The Hacker News reported that a webshell had infected more than 900 Sangoma FreePBX instances worldwide.
- Vulnerability Name: CVE-2025-64328 (Command Injection)
- Impact: Attackers exploited this vulnerability to execute remote commands and plant a webshell acting as a backdoor, gaining full control over the systems.
This incident has become a prime example of how a single vulnerability exposure can lead to large-scale infrastructure paralysis, extending beyond a specific software issue.
2. Technical Analysis of EncystPHP
While a simple webshell is like an “open back door,” EncystPHP is a “weapon” that replaces the entire building’s locks and evicts the owner. The attack flow involves three critical stages from the moment of exploitation (CVE-2025-64328) to complete system takeover.
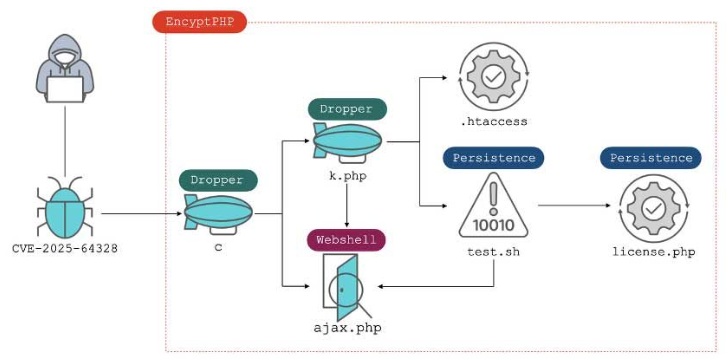
1. Multi-Stage ‘Dropper’ System: Evasion
Attackers install an initial dropper named c through the vulnerability. This c then creates another dropper, k.php. This sophisticated evasion technique ensures that even if security solutions detect the first dropper, subsequent droppers survive to continue the attack.
2. ‘chmod 000’ Lockdown: Self-Protection
The most alarming part of Figure 1 is the flow leading to the .htaccess and test.sh files. Immediately after installation, the webshell executes a chmod 000 command on itself, stripping away its own file permissions. This prevents administrators or security tools from reading, modifying, or deleting the file—effectively creating an undeletable backdoor.
3. Database Intrusion and Account Manipulation (Persistence)
In the final stage, the webshell parses the system configuration file (freepbx.conf) to steal DB credentials. It then accesses the database directly via the ajax.php webshell to intercept administrator information while deleting or altering legitimate user accounts to maintain absolute control.
3. Response Guide: Combining Real-Time Monitoring and Sigma Rules
The security expert group SOC Prime has analyzed the tactics of the EncystPHP attack and released a response guide.
- Real-Time File Monitoring: Check for newly created files named
k.php,c,ajax.php,test.sh, orlicense.php. These are often disguised as harmless image or license files. It is critical to immediately detect any new files created in writable web server directories. - Tracking ‘Unreadable’ Files: In a Linux environment, any PHP file with permissions set to
----------(000) that cannot be opened even by an administrator is a 99% indicator of infection. - Abnormal Processes: If a web server (e.g.,
httpdornginx) suddenly reads/etc/freepbx.confor sends large amounts of data to an unfamiliar external IP, the network must be disconnected immediately. - Behavior-Based Identification: Even if a file is obfuscated, its intent can be identified by matching it against attack behavior formulas (Sigma Rules) recorded in system logs.
4. Real-Time Detection and Handling is the Key, Not Post-Analysis
The conclusion from the analysis of the EncystPHP hacking incident is clear: the success of webshell defense depends on detecting and handling the webshell the very moment it is uploaded.
Before advanced webshells like EncystPHP settle into a server and begin malicious activities, the threat must be judged and neutralized at the upload stage. Proactive real-time response, which prevents an attacker from issuing even a single command, is the most reliable way to protect a company’s core assets from weaponized webshells.
5. Explore More Web Shell Threat Cases
- Linux Security Alert: Cookie PHP Web Shells (MS Report)
- Dell WMS Vulnerability: Defending Against JSP Webshells
- ASP.NET Web Shell Threats Targeting IIS Servers (UAT-8099 Case Study)
- BeyondTrust Flaw Used for Web Shells, Backdoors, and Data Exfiltration
- Web Shells and Lateral Movement
- Godzilla Webshell: A Growing Cybersecurity Threat to Healthcare
- The Evolution of the China Chopper
- APT41’s Cyber Espionage Campaign: Web Shells at the Core of Network Infiltration
6. Sources
- Analysis Report: Fortinet – Unveiling the Weaponized Web Shell EncystPHP
- Analysis Report: SOC Prime – Weaponized Web Shell Analysis
- News: The Hacker News – 900+ Sangoma FreePBX Instances Compromised in Ongoing Web Shell Attacks
- Real-Time Detection Solution: Why WSS?