Linux Security Alert: Cookie PHP Web Shells (MS Report)
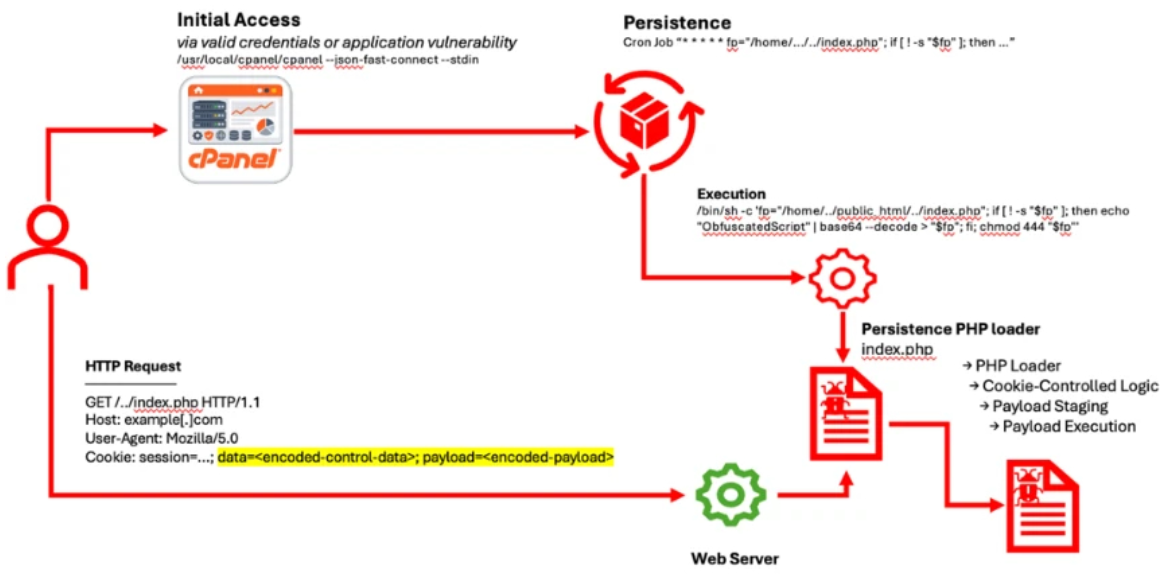
A recent Microsoft report details the rise of persistent PHP web shells on Linux that leverage Cron for longevity and utilize cookies for remote execution.
On April 03, 2026, the Microsoft Defender Security Research Team shared a critical report. It details how attackers use HTTP cookies to control PHP web shells on Linux servers. This new “stealth” malware bypasses traditional logs. It also stays active even after you try to remove it.
1. Why Attackers Use HTTP Cookies for PHP Web Shell Control
Most web shells show commands in URL parameters or request bodies. Security tools like Web Application Firewalls (WAFs) flag these easily. Consequently, attackers now hide their control logic inside the $_COOKIE variable.
The Strategic Advantages
- Stealthy Execution: Malicious code stays “dormant” during normal site visits. It only starts when a request has a specific cookie value.
- Natural Blending: Cookie values look like normal session data. Therefore, they blend perfectly into regular web traffic.
- No Extra Parsing: PHP handles cookies automatically. This means attackers pass instructions directly into the server. As a result, they avoid extra code that might trigger alerts.
2. 3 Deployment Methods of Cookie-Based Web Shells
Microsoft found three main ways attackers deploy these shells. Each method has a different goal:
- The Obfuscated Loader: This model uses many layers of encoding. It waits for a specific cookie. Then, it runs a second, more powerful attack.
- Segmented Data Reconstruction: This is a very advanced method. The attacker sends small data pieces through cookies. The script reassembles these pieces into working tools like file managers.
- The Marker Trigger: This is a simple but effective “switch.” A specific cookie value tells the script to upload files or run commands immediately.
3. Linux Persistence: How Web Shells Use Cron Jobs for Self-Healing
Finding the shell is only half the battle. These web shells are very hard to delete because they “heal” themselves.
- Initial Access: First, attackers enter using stolen passwords or unpatched bugs.
- The Cron Job Loop: Next, they set up a cron job. This is a scheduled task in Linux.
- Automatic Re-creation: You might find and delete the PHP shell. However, the cron job simply creates a new copy of the malware later. This creates a permanent doorway for attackers.
4. Neutralizing Persistent Web Shells with Web Server Safeguard
Basic security measures often fail against ‘self-healing’ threats. WSS (Web Server Safeguard) provides the deep server-side monitoring necessary to neutralize these persistent attacks.
Real-Time Monitoring
WSS watches web folders 24/7. When a cron job tries to recreate a deleted shell, WSS detects the file creation instantly. This immediate action breaks the persistence cycle of “self-healing” malware.
Hybrid Detection
WSS identifies web shells by scanning file source code through a powerful hybrid engine. It combines signature-based detection for known threats with AI-driven detection to uncover new, sophisticated patterns in cookie-based attacks.
Security Intelligence (LLM-Powered Briefing)
WSS features security-specific LLM, fine-tuned by UMV. Consequently, the system provides logical explanations in plain language, answering “Why was this detected?” instantly. This creates a 24/7 managed security environment, acting as if a top-tier analyst resides right beside you.
5. Linux Security Checklist: Preventing Persistent PHP Web Shells
Microsoft recommend these steps:
- Use MFA: Always turn on Multi-Factor Authentication for your hosting panels and SSH.
- Audit Cron Jobs: Check your scheduled tasks regularly. Look for any routines you did not create.
- Harden Your Settings: Limit what your web server can do. Block unnecessary shell commands.
- Employ AI-Powered Real-Time Detection: Incorporate an AI-driven detection and quarantine system for malicious web shells or URLs. This ensures that sophisticated threats bypassing your external defenses can be identified and contained through intelligent, real-time analysis.
6. WSS: Your Ultimate Defense Against Persistent Linux Web shells
Modern attackers no longer rely on complex exploits; they weaponize your own server tools against you. WSS (Web Server Safeguard) neutralizes these stealthy threats through AI-driven, real-time monitoring, ensuring that even the most persistent “self-healing” malware has nowhere to hide. Build a proactive defense that stays one step ahead.
