BeyondTrust Flaw Used for Web Shells, Backdoors, and Data Exfiltration
Recently, critical vulnerabilities were discovered in BeyondTrust solutions, which are responsible for enterprise privileged access management and remote support. This incident, where a solution designed to strengthen security instead became the gateway for hacking, provides a deep dive into the sophisticated threat of web shells and the importance of proactive defense.
1. Incident Overview and Background
On February 18, 2026, global security media outlets warned that the latest vulnerabilities found in BeyondTrust product lines were being actively exploited in real-world attacks. Attackers precisely targeted flaws in core infrastructure used by enterprises to manage remote work environments and system controls.
2. In-depth Vulnerability Analysis: CVE-2024-12356 & CVE-2026-1731
This situation escalated due to a chain of security flaws bypassing existing patches rather than a single defect.
| Vulnerability ID | CVSS Score | Key Characteristics | Risk Analysis |
| CVE-2024-12356 | 9.8 (Critical) | Insufficient WebSocket input validation | Allows Unauthenticated Remote Code Execution (RCE) |
| CVE-2026-1731 | 9.9 (Critical) | Version parsing and Command Injection | Bypasses existing security patches to hijack system privileges |
Attackers exploited CVE-2026-1731, another path within the same endpoint, to neutralize defenses even when patches for the vulnerability discovered in late 2024 were already applied.
3. Web Shell Attack Scenario
Beyond simple intrusion, here is the overall attack flow illustrating how attackers parasitize and maintain a continuous threat within the system:
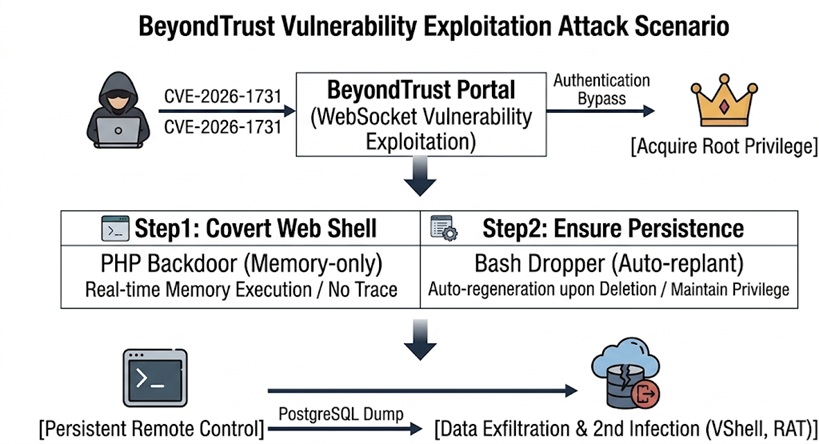
- Initial Infiltration and Privilege Escalation: Attackers neutralize the security solution’s perimeter through the CVE-2026-1731 vulnerability and seize Root privileges of the server.
- Dual-Track Web Shell Deployment:
- PHP Backdoor: Operates in memory without leaving files on the disk, neutralizing conventional file-based antivirus (AV) scans.
- Bash Dropper: Even if an administrator finds and deletes a web shell file, this dropper immediately replants it in the background to restore the attack path.
- Persistent Control Acquisition: Using the secured root privileges and web shell channels, attackers maintain a connection with an external C2 server, achieving a state of “total takeover” where they can execute follow-up commands at any time.
4. Why Security Patches Alone Are Not Enough
Many administrators rest easy assuming that applying a vulnerability patch resolves everything. However, as seen in this case, post-incident response has clear limitations when an attack is already underway:
- Substantial Data Theft: Attackers who successfully installed web shells carried out critical information theft, including compressing internal data via system commands and dumping entire PostgreSQL databases to external servers.
- Bridgehead for Secondary Infection: Using secured privileges, they install additional Remote Access Trojans (RATs) such as VShell and Spark RAT to move toward taking over the entire network. This escalates beyond a simple web server hack to a potential collapse of the entire corporate network.
5. Essential Need for Real-Time Detection-Based Proactive Defense
The BeyondTrust case offers a clear lesson. In an environment where even security solutions can be targets, we can no longer rely solely on perfect blocking. The focus must now shift to controlling “post-intrusion behavior.”
- Necessity of Real-Time Monitoring: All processes of file creation, modification, and deletion within the web server must be monitored in real-time to immediately block unauthorized web shell deployment.
- Precision Analysis at the Source Code Level: It is urgent to adopt specialized solutions that analyze the malicious intent of the code itself, rather than the file’s appearance, to catch even variant web shells.
Ultimately, the core of security is speed. Real-time detection, which catches the moment before an attacker can establish a foothold through a web shell, is the final line of defense to protect a company’s valuable assets.
6. Explore More Web Shell Threat Cases
- EncystPHP Webshell Seizes 900 Servers Worldwide
- Linux Security Alert: Cookie PHP Web Shells (MS Report)
- Dell WMS Vulnerability: Defending Against JSP Webshells
- Web Shells and Lateral Movement
- Godzilla Webshell: A Growing Cybersecurity Threat to Healthcare
- The Evolution of the China Chopper
- APT41’s Cyber Espionage Campaign: Web Shells at the Core of Network Infiltration
