Dell WMS Vulnerability: Defending Against JSP Webshells
Recent security threats have evolved into “Attack Chains.” Instead of relying on a single exploit, hackers now link multiple vulnerabilities to move from low-level access to full system control.
The security breach of Dell Wyse Management Suite (WMS), reported on March 23, 2026, is a prime example of this dangerous trend. In this post, we analyze how this attack works and how you can protect your servers from the final stage of the exploit: Webshell injection.
1. Incident Overview: Critical Vulnerabilities Discovered in Dell WMS
According to a report by the security firm ‘PT Security,’ two critical vulnerabilities capable of privilege escalation and Remote Code Execution (RCE) were discovered in WMS.
- CVE-2026-22765 (CVSS 8.8): A privilege escalation flaw that allows low-privileged users to seize full administrative rights.
- CVE-2026-22766 (CVSS 7.2): A Remote Code Execution (RCE) flaw that leverages administrative privileges to execute malicious code.
Dell released WMS version 5.5 in late February to address these flaws; however, administrators who have not yet updated remain exposed to significant risk.
2. Attack Scenario: How Systems Are Compromised
Attackers use a meticulous, step-by-step approach to neutralize defense systems
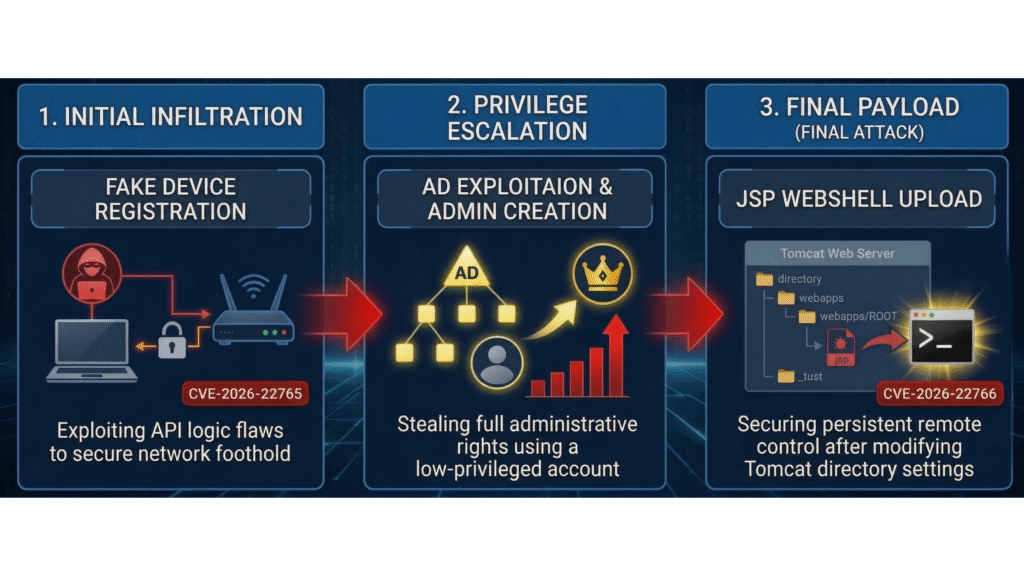
- Initial Infiltration: Exploiting logical flaws in the API to register fake devices and establish a foothold within the internal network.
- Privilege Escalation: Exploiting Active Directory (AD) paths to create administrator-level accounts and seize system control.
- Final Payload: Modifying the Tomcat web root directory settings and uploading a ‘JSP Web shell’ to execute remote commands.
3. Strategic Response: Breaking the Attack Chain with Web Server Safeguard
The core highlight of this incident lies in the attacker’s final action after escalating to administrative privileges. To achieve complete system takeover and remote control, the tool of choice was ultimately a Webshell.
Software vulnerabilities (CVEs) are discovered constantly. Attackers often succeed in infiltrating systems by exploiting the window of time when administrators find it difficult to apply every patch in real-time. However, what if we could block the execution of the webshell at the final stage, even after a successful intrusion?
To stop a sophisticated attack, you need a Web Server Safeguard (WSS).
Here is how it protects you:
- Real-time Web Root Monitoring: WSS provides real-time detection at the the moment an attacker attempts to modify Tomcat directory settings or upload a webshell.
- Blocking Abnormal File Creation: It immediately isolates malicious JSP files entering through vulnerabilities like CVE-2026-22766, fundamentally blocking the ‘command execution’ phase of the attack chain.
- Continuous Visibility: Moving beyond simple file scanning, it analyzes abnormal behavior within the web server and sends instant alerts to administrators.
4. Action Plan and Conclusion
- Immediate Update: Organizations using Dell WMS must upgrade to version 5.5 or higher immediately.
- Establish Hierarchical Defense: In addition to patch management, it is essential to implement a dedicated webshell detection solution (WSS) that monitors post-infiltration activities.
The most effective way to break the link between minor flaws is to neutralize the webshell—the final stage of the attack. Is your web server protected against this ultimate threat?

5. Explore More Web Shell Threat Cases
- EncystPHP Webshell Seizes 900 Servers Worldwide
- Linux Security Alert: Cookie PHP Web Shells (MS Report)
- ASP.NET Web Shell Threats Targeting IIS Servers (UAT-8099 Case Study)
- BeyondTrust Flaw Used for Web Shells, Backdoors, and Data Exfiltration
- Web Shells and Lateral Movement
- Godzilla Webshell: A Growing Cybersecurity Threat to Healthcare
- The Evolution of the China Chopper
- APT41’s Cyber Espionage Campaign: Web Shells at the Core of Network Infiltration
6. Reference and Source
- https://www.boannews.com/media/view.asp?idx=142840&kind=4&search=title&find=%BB%E7%BC%D2%C7%D1
- https://www.dell.com/support/kbdoc/en-us/000429141/dsa-2026-103-security-update-for-dell-wyse-management-suite-wms-for-multiple-vulnerabilities
- https://swarm.ptsecurity.com/business-logic-and-chains-unauthenticated-rce-in-dell-wyse-management-suite/