UMV Security Blog
Updates on web server security and web hacking from around the world
Search UMV’s website:
Suspected North Korean Hackers Linked to Large-Scale Golf Club Data Breach
More Than 100,000 Customer Records Exposed Following Website Compromise Key Takeaways More than 100,000 customer records were reportedly exposed Malware was allegedly inserted…
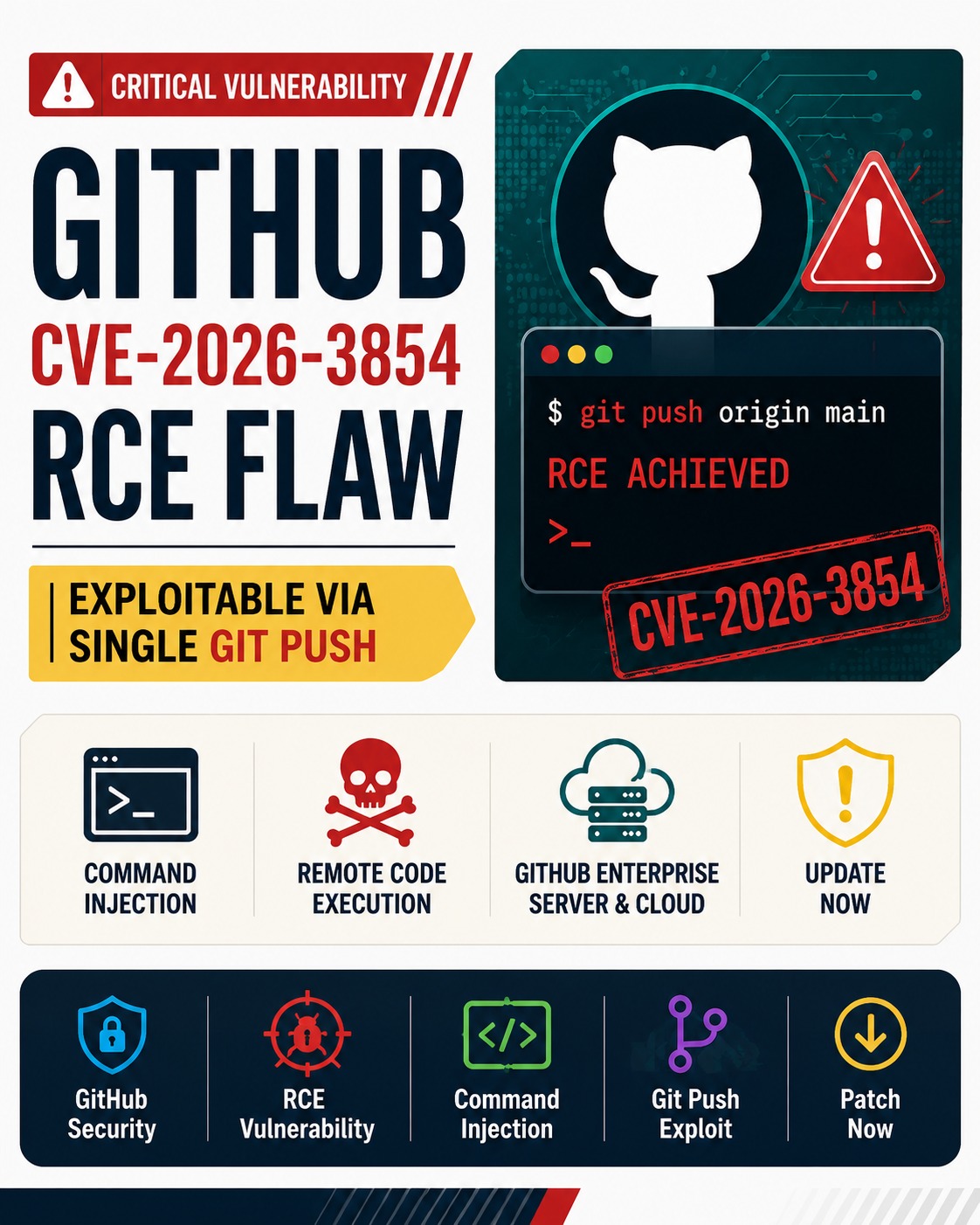
GitHub CVE-2026-3854 Enables Remote Code Execution via Single Git Push
GitHub CVE-2026-3854 Enables Remote Code Execution via Single Git Push Key Takeaways CVE-2026-3854 enables remote code execution (RCE) through a single git…
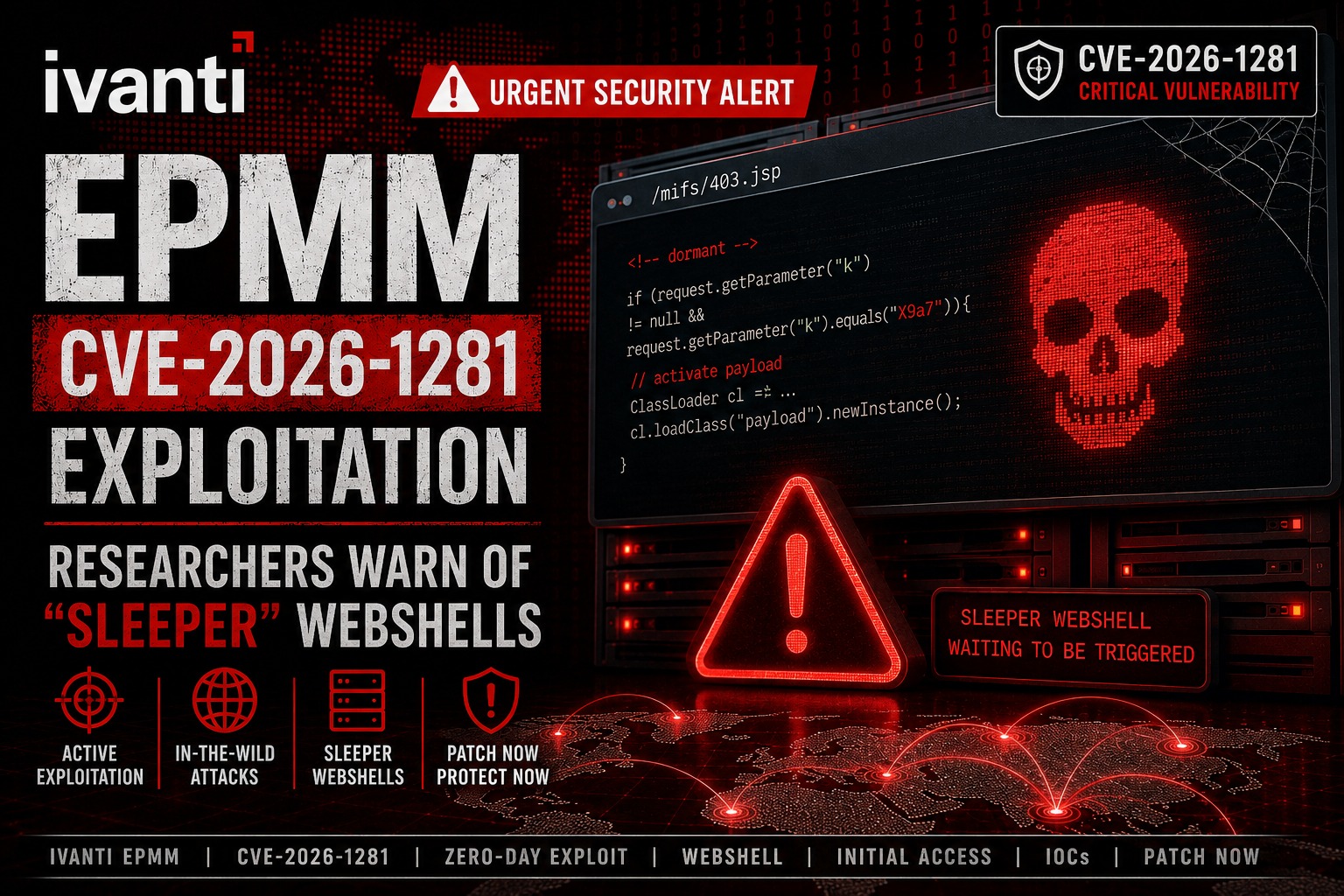
Ivanti EPMM Vulnerability Exploited to Deploy Sleeper Webshells
Ivanti EPMM Vulnerability Exploited to Deploy Sleeper Webshells 1. Ivanti EPMM CVE-2026-1281 Exploitation Overview Security researchers have identified campaigns leveraging this flaw…
WSS ZYON AI: Achieving 100% Web Shell Detection
WSS ZYON AI: Achieving 100% Web Shell Detection in Next-Generation Web Security Recent surges in web shell-based ransomware and advanced persistent…
EncystPHP Webshell Seizes 900 Servers Worldwide
EncystPHP Webshell Seizes 900 Servers Worldwide Earlier this year, a severe security incident occurred on FreePBX, an open-source IP PBX platform….
Innovating Security ‘Judgment’: WSS ZYON AI
Innovating Security ‘Judgment’: The Future of Autonomous Security Realized by ZYON AI In the face of exponentially increasing web traffic and…
Linux Security Alert: Cookie PHP Web Shells (MS Report)
Linux Security Alert: Cookie PHP Web Shells (MS Report) A recent Microsoft report details the rise of persistent PHP web shells…
Dell WMS Vulnerability: Defending Against JSP Webshells
Dell WMS Vulnerability: Defending Against JSP Webshells Recent security threats have evolved into “Attack Chains.” Instead of relying on a single…
ASP.NET Web Shell Threats Targeting IIS Servers (UAT-8099 Case Study)
ASP.NET Web Shell Threats Targeting IIS Servers (UAT-8099 Case Study) Despite rapid advancements in security technology, web shells remain the preferred…
UMV Obtains GS Certification Class 1 for ‘WSS 3.0’ with AI Agent
UMV Obtains GS Certification Class 1 for ‘WSS 3.0’ with AI Agent UMV (CEO Yun Sung Bang) has officially launched ‘WSS…
BeyondTrust Flaw Used for Web Shells, Backdoors, and Data Exfiltration
BeyondTrust Flaw Used for Web Shells, Backdoors, and Data Exfiltration Recently, critical vulnerabilities were discovered in BeyondTrust solutions, which are responsible…
AI Security WSS: UMV & Handong Global University MOU
AI Security WSS: UMV & Handong Global University MOU UMV is setting a new standard for web server security. By integrating…
“The security chain is only as strong as its weakest link.”