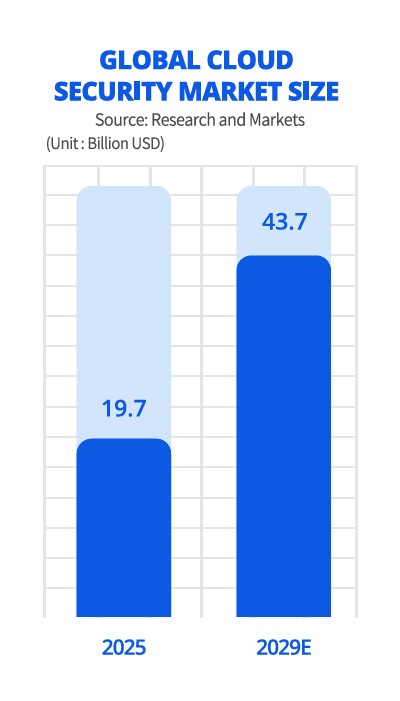
2026 Cloud Trend : Security is the New Standard of Excellence
In 2026, the criteria for cloud adoption have shifted from cost-efficiency to uncompromising security.
Following major security breaches at large-scale enterprises like Coupang, the market landscape has transformed. Cloud providers are no longer just infrastructure vendors; they are evolving into specialized security firms. Here is why “Security Prowess” is now the ultimate competitive edge.
1. 58% Surge in Security Spending: “Security is the Business Enabler”
According to a survey by Samsung SDS of 600 IT decision-makers, 58% of enterprises plan to increase their security budgets this year.
- Shift in Executive Mindset: Executives no longer view security as a ‘back-burner cost.’ Instead, they treat it as a strategic asset in ‘Door-Opening’ strategies to win new, high-value clients.
- Strong Industry Consensus: With only 3% of companies planning to reduce spending, the industry-wide commitment to strengthening security is undeniable.
2. Security: The Prerequisite for AI Innovation
As the era of Generative AI matures, the status of security has reached new heights. Enterprises are racing to build defense systems that match the speed of their AI deployments.
- Top 3 Investment Priorities: Security ranks as the third-highest investment priority (after Generative AI at 75% and AI Agents at 74%).
- The “Safe AI” Mandate: 67% of companies increasing their GenAI investments are simultaneously boosting their security spending, signaling that safety is a non-negotiable prerequisite for AI business models.
3. Security Strategies of Leading Korean Cloud Providers
Major Korean tech giants are integrating infrastructure management with specialized security capabilities.
| Company | Key Security Strategy | Core Features |
| Samsung SDS | Standardized Security Consulting | Offers vulnerability diagnostics and Dark Web leak monitoring to all clients. |
| KT | Secure Public Cloud | Enhances physical and regulatory security by ensuring data stays within domestic boundaries. |
| LG CNS | AI Security Solutions (SecuXper AI) | Specialized defense against data leaks and breaches occurring through Generative AI usage. |
4. Merging Macro Infrastructure with Micro Response
Building a sturdy castle wall (Infrastructure) is only half the battle. You must also have precision monitoring (Platforms) to detect intruders who have already slipped inside.
This is why leading MSPs (Managed Service Providers) like MegazoneCloud and Bespin Global are aggressively partnering with global security firms. A foolproof security architecture requires the combination of a “Macro Strategy” (blocking large-scale vulnerabilities) and a “Micro Response” (detecting minute configuration errors or credential leaks in real-time).
5. Security is the True Measure of Cloud Capability
Security is no longer a secondary thought—it is at the front line of business strategy. The industry-wide “all-in” on security stems from the painful lesson that without protecting customer data, growth and innovation are impossible.
At UMV Technology, we are aligned with this global shift. We protect your cloud environment through a real-time monitoring-based precision response system, ensuring your business innovation continues on the safest possible foundation.